第 2 課
What Is a Decentralized Identifier (DID)?
The building block of self-sovereign identity.

We're now entering a new era where identities are decentralized, portable, and under individual control. At the heart of this shift is a foundational concept: Decentralized Identifiers (DIDs).
Defined by the W3C (World Wide Web Consortium), the international standards body behind core web technologies like HTML and CSS, a DID is a new type of identifier that enables verifiable, self-controlled digital identities. Unlike email addresses or usernames that depend on service providers, DIDs are created and managed entirely by the user and verified cryptographically across a decentralized network.
 These identifiers form the root of your digital identity and are central to SSI systems. They not only provide login credentials, but they also allow you to prove ownership of credentials, sign messages, and interact with systems securely.
For instance, DIDs can be resolved and verified quickly on high-speed networks like the XRPL, making them ideal for time-sensitive applications such as finance or commerce.
These identifiers form the root of your digital identity and are central to SSI systems. They not only provide login credentials, but they also allow you to prove ownership of credentials, sign messages, and interact with systems securely.
For instance, DIDs can be resolved and verified quickly on high-speed networks like the XRPL, making them ideal for time-sensitive applications such as finance or commerce.
 A DID may look like a random string, but it follows a defined structure set by W3C:
A DID may look like a random string, but it follows a defined structure set by W3C:
 Each DID points to a DID Document, which functions like a digital "business card" or public profile. But instead of personal details, it contains cryptographic material and metadata needed for verification and communication.
A typical DID Document includes:
Each DID points to a DID Document, which functions like a digital "business card" or public profile. But instead of personal details, it contains cryptographic material and metadata needed for verification and communication.
A typical DID Document includes:
 Behind the scenes, DIDs work through public-key cryptography. When you generate a DID, you create a key pair: a private key (which you keep secret) and a public key (which is published in the DID Document).
When someone wants to verify your identity or a credential, they check your digital signature against your public key – automatically proving that you're the owner of the DID. (A digital signature is not a reusable thing, as the name may imply. Instead, it’s unique and a new one is created whenever a transaction is executed. We’ll get more into this later.)
Each DID also follows a method specification that describes how to perform core operations such as creation, resolution, and deactivation. Communities or networks define these methods – for instance, the xrpl method defines how XRPL-specific DIDs are anchored to the XRP Ledger.
This decentralized resolution process ensures that anyone can verify a DID's authenticity without needing permission from a central authority. So, if you issued the signature and it’s been verified, it’s now provable by anyone. See how handy this is?!
Behind the scenes, DIDs work through public-key cryptography. When you generate a DID, you create a key pair: a private key (which you keep secret) and a public key (which is published in the DID Document).
When someone wants to verify your identity or a credential, they check your digital signature against your public key – automatically proving that you're the owner of the DID. (A digital signature is not a reusable thing, as the name may imply. Instead, it’s unique and a new one is created whenever a transaction is executed. We’ll get more into this later.)
Each DID also follows a method specification that describes how to perform core operations such as creation, resolution, and deactivation. Communities or networks define these methods – for instance, the xrpl method defines how XRPL-specific DIDs are anchored to the XRP Ledger.
This decentralized resolution process ensures that anyone can verify a DID's authenticity without needing permission from a central authority. So, if you issued the signature and it’s been verified, it’s now provable by anyone. See how handy this is?!
 DIDs are more than a username: they’re a powerful tool for digital freedom.
Here's why they matter:
DIDs are more than a username: they’re a powerful tool for digital freedom.
Here's why they matter:
 These identifiers form the root of your digital identity and are central to SSI systems. They not only provide login credentials, but they also allow you to prove ownership of credentials, sign messages, and interact with systems securely.
For instance, DIDs can be resolved and verified quickly on high-speed networks like the XRPL, making them ideal for time-sensitive applications such as finance or commerce.
These identifiers form the root of your digital identity and are central to SSI systems. They not only provide login credentials, but they also allow you to prove ownership of credentials, sign messages, and interact with systems securely.
For instance, DIDs can be resolved and verified quickly on high-speed networks like the XRPL, making them ideal for time-sensitive applications such as finance or commerce.
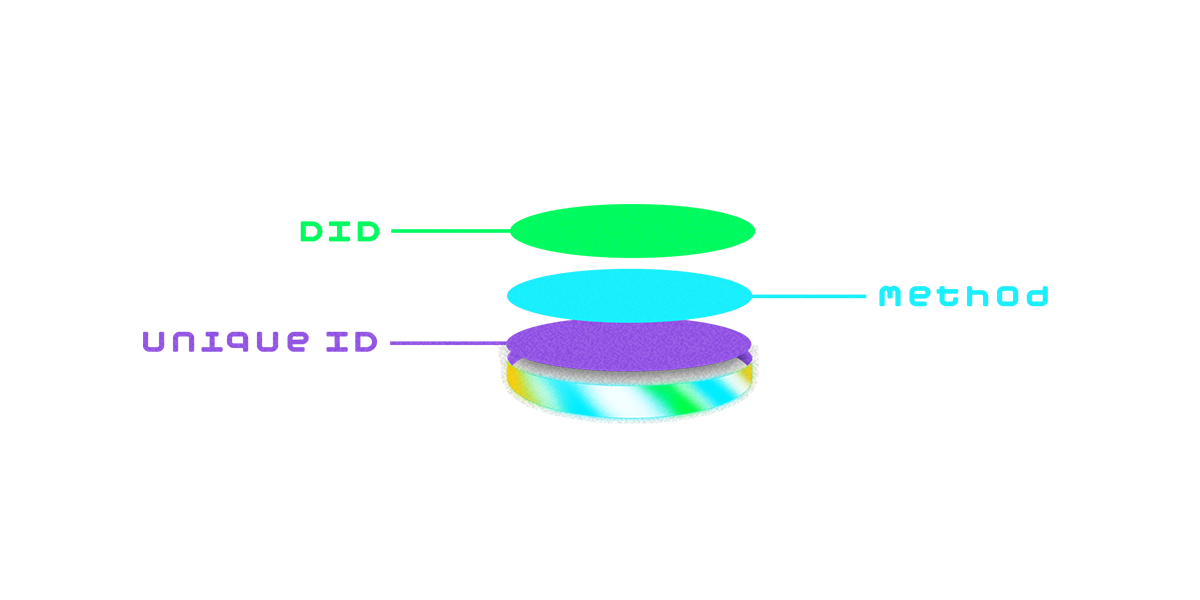
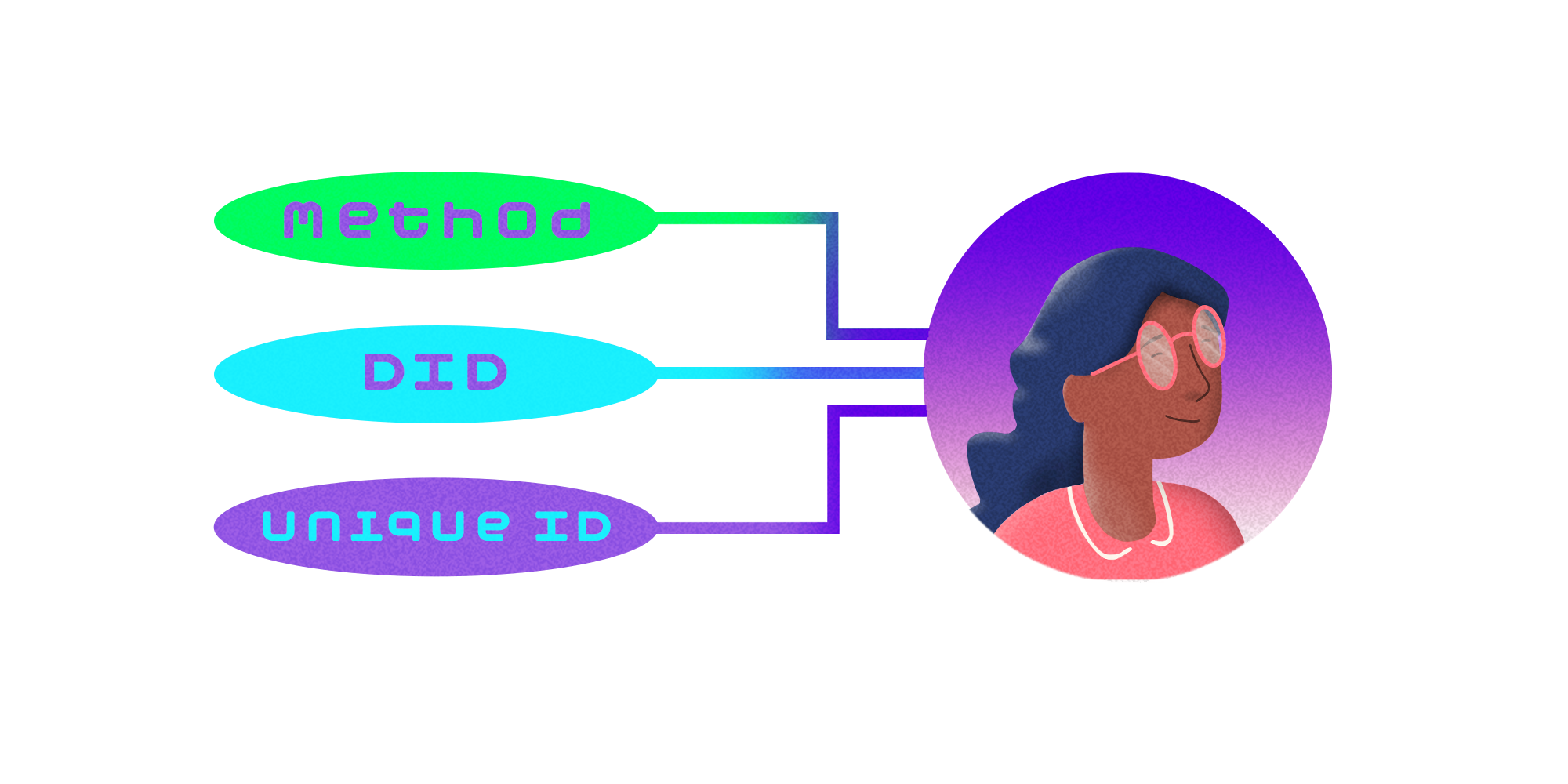
Anatomy of a DID: Structure and Syntax
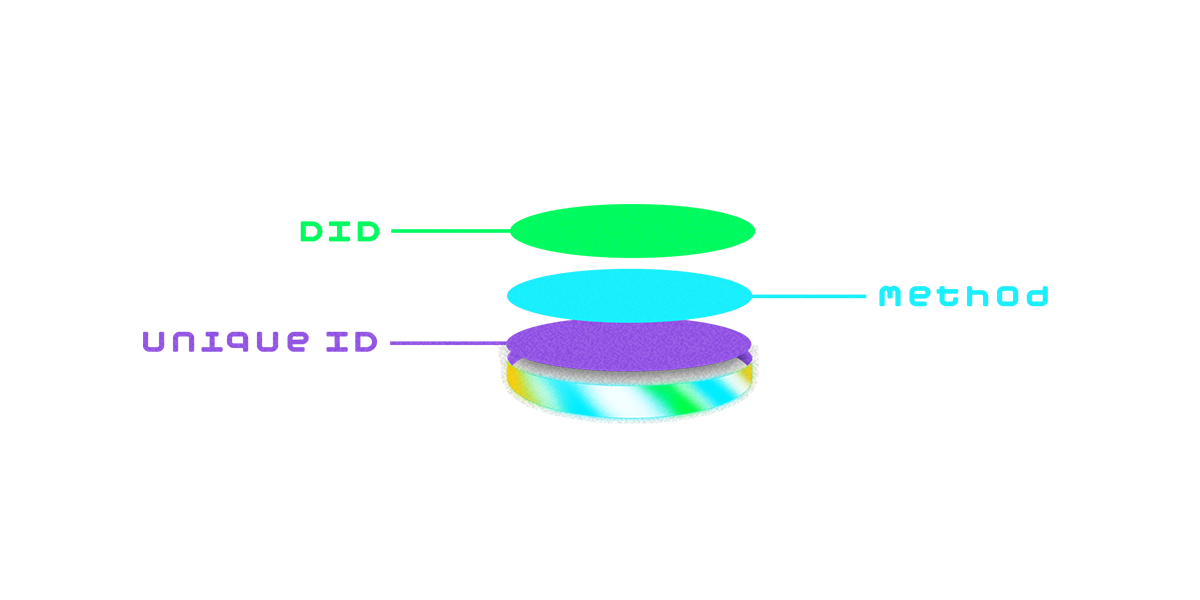 A DID may look like a random string, but it follows a defined structure set by W3C:
A DID may look like a random string, but it follows a defined structure set by W3C:
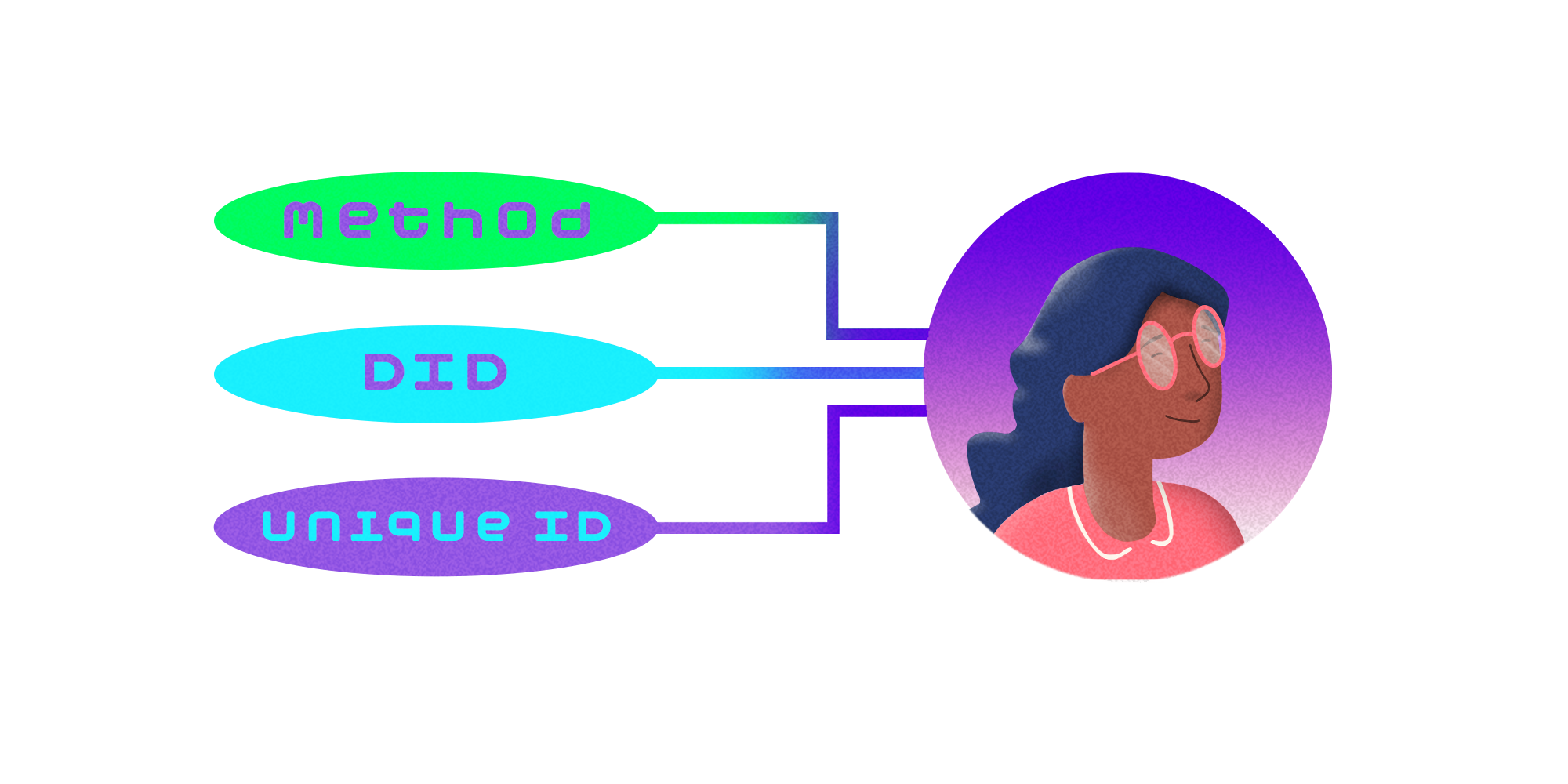
- did:method:uniqueID
- did - The required prefix indicating this is a decentralized identifier.
- method - The DID method that defines how this DID is created, resolved, and updated on a specific network or system.
- uniqueID - A unique string generated by the user, often tied to a public key or blockchain reference.
- did:xrpl:1:rAbCDefGHiJkLMn123456
- “did” is the prefix indicating that this will be a DID;
- “xrpl” is the method, indicating we’ll be working with the XRPL; and
- “1:rAbCDefGHiJkLMn123456” is the uniqueID. On the XRPL, you can think of the “1:” part as a network/version indicator, similar to how you may be familiar with how API endpoints work (e.g., query strings with “/v1/” or “/v2/” in them). While a tad confusing initially, this design actually shows a lot of forward-thinking on the part of the XRPL developers, as they needed a way to ensure future expandability and functionality.
 Each DID points to a DID Document, which functions like a digital "business card" or public profile. But instead of personal details, it contains cryptographic material and metadata needed for verification and communication.
A typical DID Document includes:
Each DID points to a DID Document, which functions like a digital "business card" or public profile. But instead of personal details, it contains cryptographic material and metadata needed for verification and communication.
A typical DID Document includes:
- Public Keys: Used to verify digital signatures and prove identity.
- Service Endpoints: URLs or addresses for interacting with the DID owner (e.g., for messaging or credential exchange).
- Metadata: Extra data such as creation time, authentication methods, or revocation information.
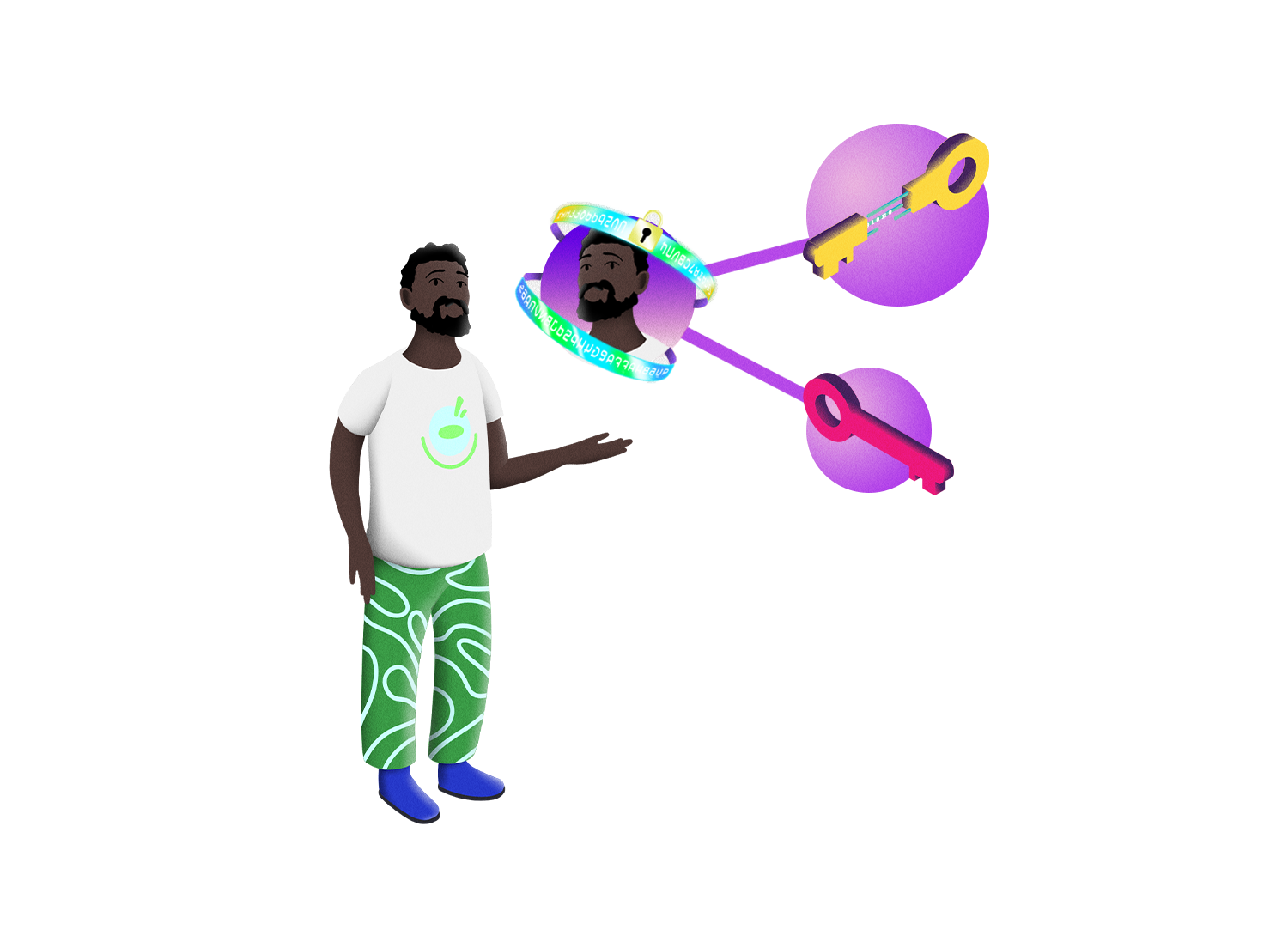
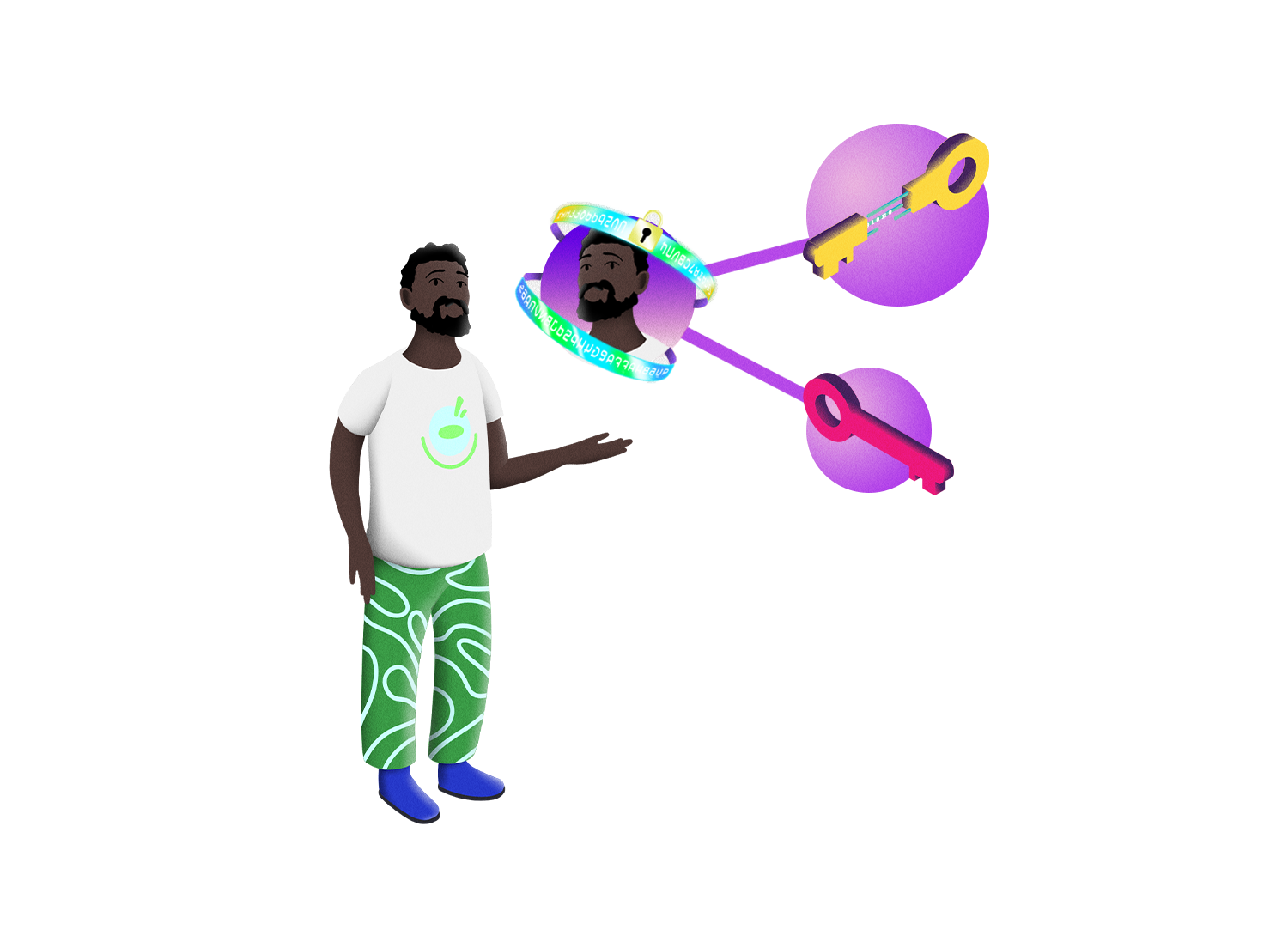 Behind the scenes, DIDs work through public-key cryptography. When you generate a DID, you create a key pair: a private key (which you keep secret) and a public key (which is published in the DID Document).
When someone wants to verify your identity or a credential, they check your digital signature against your public key – automatically proving that you're the owner of the DID. (A digital signature is not a reusable thing, as the name may imply. Instead, it’s unique and a new one is created whenever a transaction is executed. We’ll get more into this later.)
Each DID also follows a method specification that describes how to perform core operations such as creation, resolution, and deactivation. Communities or networks define these methods – for instance, the xrpl method defines how XRPL-specific DIDs are anchored to the XRP Ledger.
This decentralized resolution process ensures that anyone can verify a DID's authenticity without needing permission from a central authority. So, if you issued the signature and it’s been verified, it’s now provable by anyone. See how handy this is?!
Behind the scenes, DIDs work through public-key cryptography. When you generate a DID, you create a key pair: a private key (which you keep secret) and a public key (which is published in the DID Document).
When someone wants to verify your identity or a credential, they check your digital signature against your public key – automatically proving that you're the owner of the DID. (A digital signature is not a reusable thing, as the name may imply. Instead, it’s unique and a new one is created whenever a transaction is executed. We’ll get more into this later.)
Each DID also follows a method specification that describes how to perform core operations such as creation, resolution, and deactivation. Communities or networks define these methods – for instance, the xrpl method defines how XRPL-specific DIDs are anchored to the XRP Ledger.
This decentralized resolution process ensures that anyone can verify a DID's authenticity without needing permission from a central authority. So, if you issued the signature and it’s been verified, it’s now provable by anyone. See how handy this is?!
 DIDs are more than a username: they’re a powerful tool for digital freedom.
Here's why they matter:
DIDs are more than a username: they’re a powerful tool for digital freedom.
Here's why they matter:
-
- User Control: You create and manage your identity without needing approval from any organization.
- Performance: Blockchain is 24/7, global, and can be automated through smart contract programming. This means it is much more efficient than traditional systems.
- Privacy: Only share what's necessary; your identity isn't tied to a central profile.
- Interoperability: DIDs work across different systems and platforms. For instance, your identity could be tied to both a social media platform and a financial application.
- Censorship Resistance: Because no central authority controls DIDs, they can't be easily taken down or blocked.
- Security: Blockchain technology’s public key cryptography makes DIDs highly secure and verifiable.