레슨 6
Capstone: Designing a DID Use Case
Turn decentralized identity theory into real-world design.

You've explored the building blocks of decentralized identity: DIDs, verifiable credentials, and the XRPL ecosystem that powers them. Now it's time to put your knowledge into action. Or simply read through this lesson as (1) hypothetical inspiration and/or (2) a handy review of how one might apply the lessons of this course in a practical, real-world way.
This capstone lesson challenges you to design your own DID use case using XRPL's identity features. Your goal is to show how identity can be decentralized, trusted, and compliant – without compromising user privacy or application speed.
Whether you're passionate about fintech, supply chains, healthcare, education, or creative assets, this is your chance to solve a real-world problem using the XRPL identity stack.
 Start by selecting a practical identity challenge that interests you. Here are a few possibilities:
Start by selecting a practical identity challenge that interests you. Here are a few possibilities:
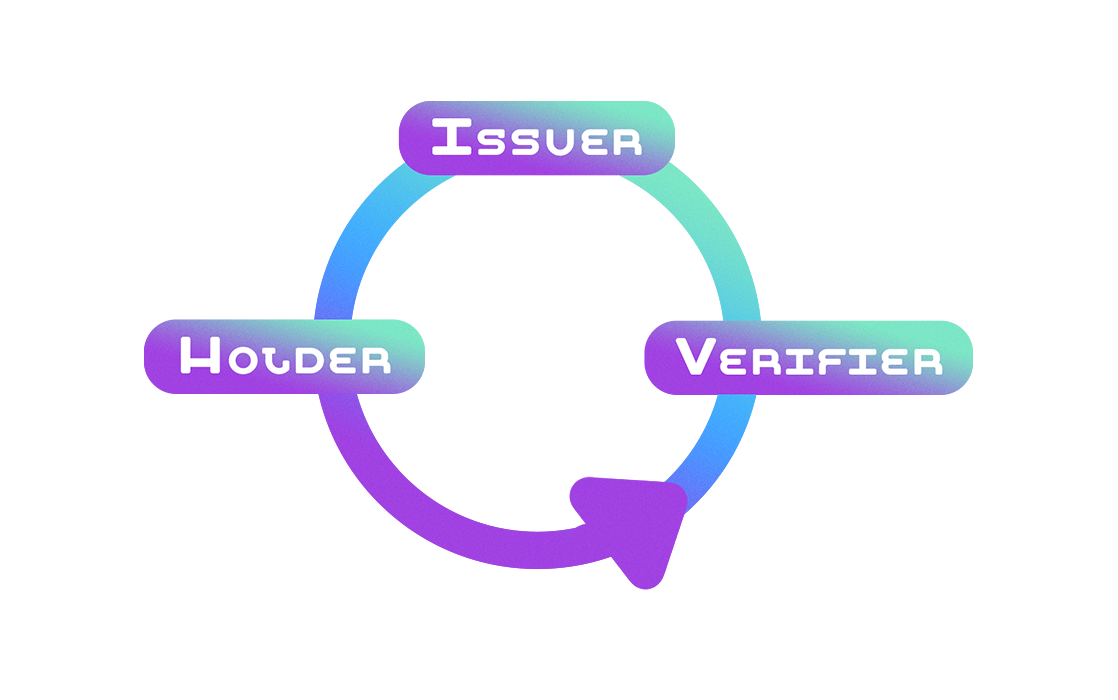
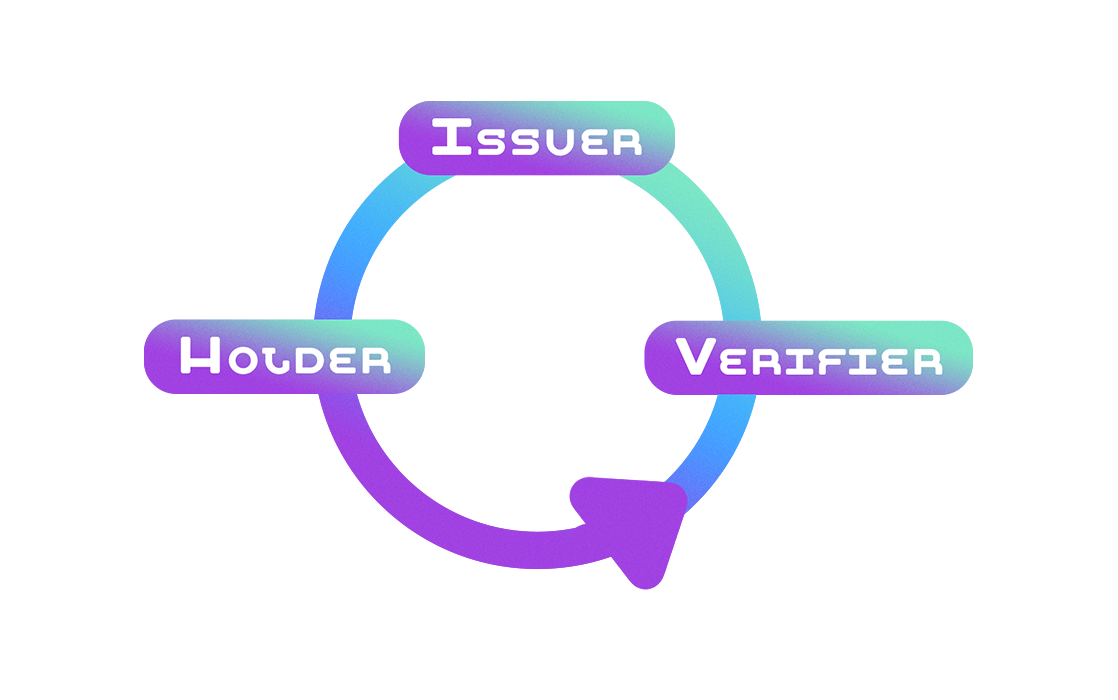
 Now map your scenario onto the verifiable credential model. Every use case has three key roles:
Now map your scenario onto the verifiable credential model. Every use case has three key roles:
 By walking through this process, you've created more than a diagram – you've shown how decentralized identity can solve problems today.
You've also shown how XRPL supports:
By walking through this process, you've created more than a diagram – you've shown how decentralized identity can solve problems today.
You've also shown how XRPL supports:
Define the Identity Scenario
 Start by selecting a practical identity challenge that interests you. Here are a few possibilities:
Start by selecting a practical identity challenge that interests you. Here are a few possibilities:
- Decentralized KYC - Can DIDs and VCs streamline onboarding in finance?
- NFT Provenance - Can credentials prove who created and owns digital art?
- Diploma Verification - Can schools issue credentials to grads that employers can instantly verify?
- Healthcare Access - Can patients carry portable proof of insurance or vaccination?
 Now map your scenario onto the verifiable credential model. Every use case has three key roles:
Now map your scenario onto the verifiable credential model. Every use case has three key roles:
- Issuer - Who is trusted to issue the credential? (e.g., a government, bank, or school)
- Holder - Who owns and manages the credential? (e.g., a user, artist, student)
- Verifier - Who needs to check the credential? (e.g., a DEX, gallery, employer)
- What kind of credential is issued?
- Where is it stored?
- How is it verified – on-chain, off-chain, or hybrid?
Present Your Model with XRPL in Action
Now bring it all together. Use what you've learned about XRPL's DID and credential stack to explain:- How your use case uses did:xrpl
- How credentials are issued and validated using XLS-70
- How compliance is enforced with XLS-80 or XLS-81 (if relevant)
- How XRPL's speed and scalability improve user experience
- How privacy is preserved through selective disclosure
 By walking through this process, you've created more than a diagram – you've shown how decentralized identity can solve problems today.
You've also shown how XRPL supports:
By walking through this process, you've created more than a diagram – you've shown how decentralized identity can solve problems today.
You've also shown how XRPL supports:
- Global standards (W3C DIDs, VCs)
- Privacy-first verification
- Regulatory alignment
- Real-time transactions
- Interoperability and openness